Door Access + Timekeeping with Payroll System
Biometrics - Biometric security systems are designed to identify individuals by measuring unique physical patterns, and matching them to stored information. These systems can read fingerprints, faces, palm prints, even retinas, to allow access to restricted areas.
There are two main biometric classifications:
1.) Physiological – which relate to the shape of the body, such as fingerprints, eyes, and faces.
2.) Behavioural – which relate to behaviours such as voice recognition or keystroke dynamics.
Although previously, biometrics had an unreliable reputation, progressions in technology are now making this platform one of the most practical and user-friendly systems available.
Biometrics can remove any discrepancies created by human error. Passwords can be forgotten; keys, cards and tokens can be lost, stolen, damaged or borrowed by others. Biometrics provide trouble-free, easy to use solutions to keep sites safe and secure.
Which seamlessly integrates with most existing access control systems, securely stores up to 10,000 individual fingerprints (Depends on model) and continues to work in harsh environments and extreme temperatures. Ideal for many applications, this IP rated device can read fingerprints that other readers would not register – wet, dirty, or through powder, cream, oil or even latex gloves. It can also recognise the difference between a real and a spoof fingerprint by measuring the difference in light passing through the sensor.
Biometric Payroll System - Biometric Time Attendance Systems for Government Office, Fingerprint Time Attendance system for Employee Time Record System. Biometric Attendance software for Biometrics or Fingerprint Attendance System. Biometric Time Attendance software generates all Time Attendance Reports. The Trademesoft Biometric Payroll Software is useful and Customizable for Biometric Attendance system, Biometric Time Attendance for Office Government Factory Retail Shops Hotel Hospital Clinics. Support available in the Philippines. The Trademesoft Biometric Payroll Software available with Fingerprint systems Scanner, CARD Reader, Biometric fingerprint time attendance system for fingerprint based time and attendance solutions. Fingerprint or show card products for time attendance and access control system. Learn more info, just click here
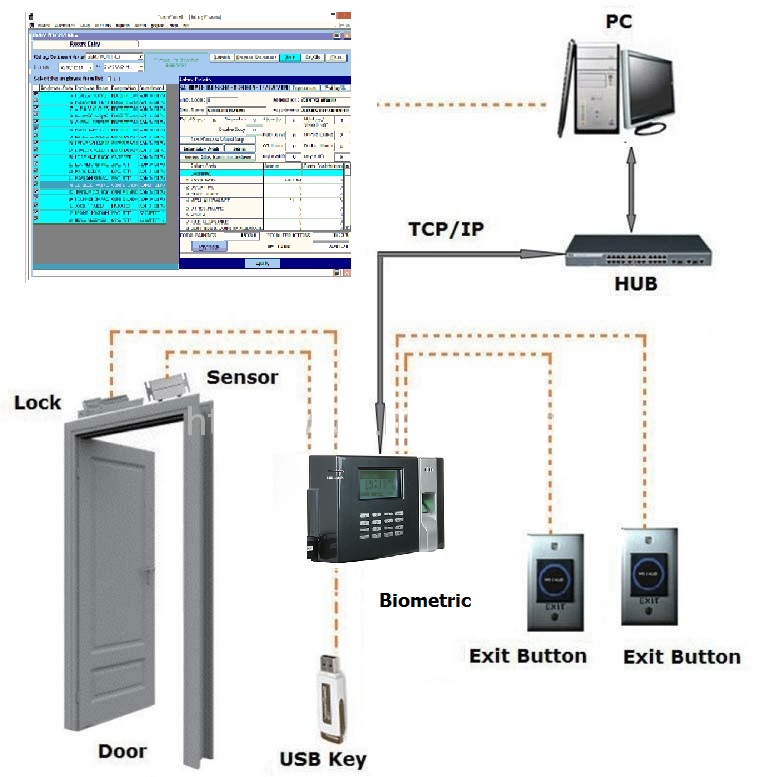
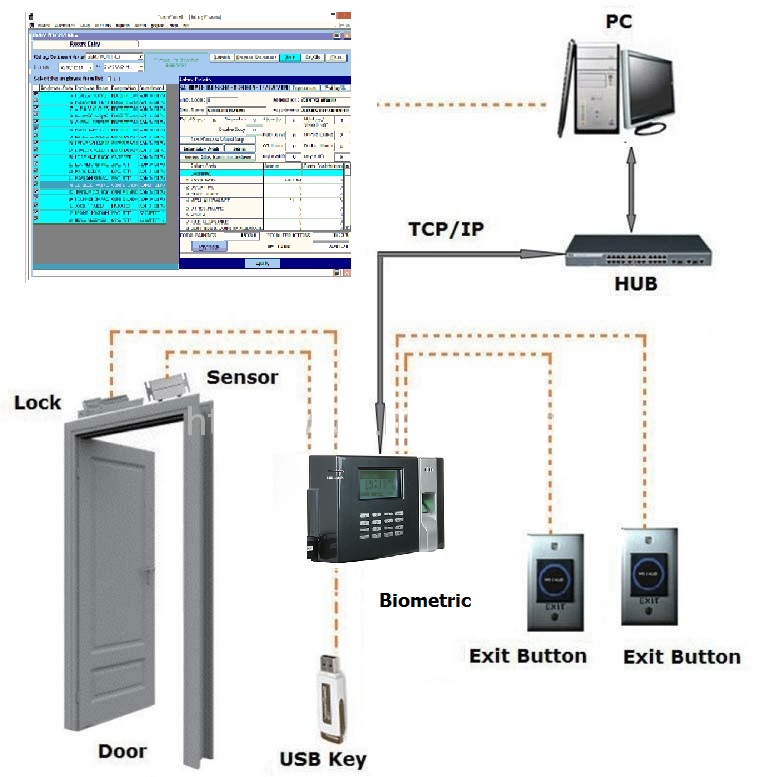
Door Access Control - Access control decisions are made by comparing the credential to an access control list. This lookup can be done by a host or server, by an access control panel, or by a reader. The development of access control systems has seen a steady push of the lookup out from a central host to the edge of the system, or the reader. The predominate topology circa 2009 is hub and spoke with a control panel as the hub and the readers as the spokes. The lookup and control functions are by the control panel. The spokes communicate through a serial connection; usually RS485. a
Some manufactures are pushing the decision making to the edge by placing a controller at the door. The controllers are IP enabled and connect to a host and database using standard networks
Access control refers to exerting control over who can interact with a resource. Often but not always, this involves an authority, who does the controlling. The resource can be a given building, group of buildings, or computer-based information system. But it can also refer to a restroom stall where access is controlled by using a coin to open the door.
Access control is, in reality, an everyday phenomenon. A lock on a car door is essentially a form of access control. A PIN on an ATM system at a bank is another means of access control. The possession of access control is of prime importance when persons seek to secure important, confidential, or sensitive information and equipment
Item control or or electronic key is an area within (and possibly integrated with) an access control system which concerns the managing of possession and location of small assets or physical (mechanical) keys
Access control system operation
When a credential is presented to a reader, the reader sends the credential’s information, usually a number, to a control panel, a highly reliable processor. The control panel compares the credential's number to an access control list, grants or denies the presented request, and sends a transaction log to a database. When access is denied based on the access control list, the door remains locked. If there is a match between the credential and the access control list, the control panel operates a relay that in turn unlocks the door. The control panel also ignores a door open signal to prevent an alarm. Often the reader provides feedback, such as a flashing red LED for an access denied and a flashing green LED for an access granted.
The above description illustrates a single factor transaction. Credentials can be passed around, thus subverting the access control list. For example, Alice has access rights to the server room but Bob does not. Alice either gives Bob her credential or Bob takes it; he now has access to the server room. To prevent this, two-factor authentication can be used. In a two factor transaction, the presented credential and a second factor are needed for access to be granted; another factor can be a PIN, a second credential, operator intervention, or a biometric input.
There are three types (factors) of authenticating information:
- something the user knows, e.g. a password, pass-phrase or PIN
- something the user has, such as smart card
- something the user is, such as fingerprint, verified by biometric measurement
Passwords are a common means of verifying a user's identity before access is given to information systems. In addition, a fourth factor of authentication is now recognized: someone you know, where another person who knows you can provide a human element of authentication in situations where systems have been set up to allow for such scenarios. For example, a user may have their password, but have forgotten their smart card. In such a scenario, if the user is known to designated cohorts, the cohorts may provide their smart card and password in combination with the extant factor of the user in question and thus provide two factors for the user with missing credential, and three factors overall to allow access
If you already have an access control system in place and are looking to upgrade by adding biometrics, or if you are interested in installing a new system, please contact us here or call on +632-866-5599 (Manila, Philippines) or +6332-261-7949 (Cebu, Philippines).
 cs
cs